Overview of Secure Boot Scheme
The secure boot scheme is used to protect the legitimacy of firmware data (including bootloader and app firmware). It uses the RSA digital signature algorithm to verify the signature attached to the firmware data before loading and running the new firmware data, thereby verifying whether the firmware data is legitimate. When the secure boot scheme is enabled, the device only loads and runs firmware that is authorised by a specified private key.
Before delving into the implementation principles of secure boot, let's briefly review the boot process of ESP32-C3 as depicted in Figure 13.11.
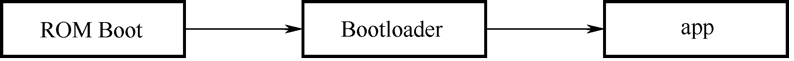
When the device is powered on, the booting process starts from ROM Boot, followed by transitioning to the Bootloader, and ultimately reaches the app firmware. ROM Boot is a fixed, executable program in the on-chip ROM that remains unalterable. Consequently, the bootloader and app firmware are the key components requiring protection. Modifying the firmware can be achieved through two methods: physical flashing, where the new bootloader and app firmware are written to the device's flash memory using a flashing tool, or OTA upgrades, which solely update the app firmware while excluding the bootloader.
So, here comes the question – how can we ensure the integrity and legitimacy of the firmware data, regardless of the method used to transmit it to the device? To address this query, we will explore two operational modes of secure boot in Section 13.4.3 and Section 13.4.4: software secure boot and hardware secure boot.
📌 Tip
There are two versions of the secure boot scheme, v1 and v2. As ESP32-C3 only supports secure boot v2, the contents in this section are applicable to secure boot v2.